Common IT Mistakes Small Businesses Make — And How to Avoid Them
Running a small business means juggling a lot at once, from…

How senate bill 820 will affect your school district
K-12 school districts are a favorite target of cybersecurity attacks. Cybersecurity incidents rose 18% in 2020 and included data breaches, phishing attacks, and ransomware. School districts must now comply with Senate Bill 820 to ensure student information and other sensitive data are protected.

Making Sure You’re up to Date on Cybersecurity
Cyberthreats are constantly evolving. But when was the last time you audited or updated your cybersecurity framework? Below, we look at how to design an effective cybersecurity strategy and offer tips on how to stay on top of the latest cybersecurity threats.

Planning safe and effective technology solutions for your schools
Protecting the technology in your school is important for the privacy of the students as well as school data and files. With hundreds of different computers and students visiting various websites all day long, it’s easy for viruses to lock up devices and/or steal data. All it takes is one bad website or phishing email for a device to become compromised.
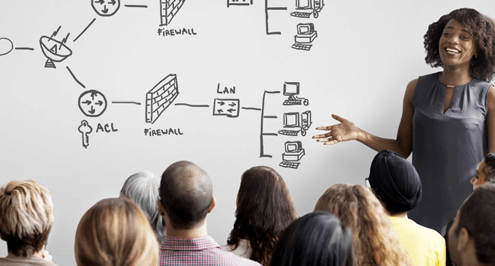
Cybersecurity Training for Employees
The majority of business is performed online in today’s hyper-connected…

How To Protect Your Business From Phishing Attacks
Phishing has become a well-known term in the world of cybercrime…

HIPAA Compliance in the Cybersecurity Age
Healthcare organizations face tough challenges regarding data security. They must abide by the mandates of HIPAA when dealing with protected health information (PHI). However, cybersecurity is a much more recent problem facing compliance. Find out how to remain compliant through cyberattacks here.

2020: Why Cybersecurity Is More Important for the Future
Cybersecurity is a major concern for business owners. As technology evolves, more devices are placed on networks, creating even greater risks and vulnerabilities. Putting the right policies and best practices in place will help combat the risks of data breaches as well diligence in ensuring they are followed.

Cybersecurity for Small Business
If you’re a small business owner, cybersecurity may seem like an unnecessary expense. Small businesses, however, are among the most targeted. Putting the right cybersecurity policies and best practices in place will reduce your chances of attack while providing the ultimate protection you deserve.